.png)
Security – Cloud Accelerator Workshop
Better understand, prioritize, and mitigate potential threats by documenting and putting in place a security strategy for teams and stakeholders.
.png.webp?width=60&height=60&name=audience%20(1).png.webp) Audience
Senior BDMs – CIO, etc., and TDMs – IT Security, IT Ops
Audience
Senior BDMs – CIO, etc., and TDMs – IT Security, IT Ops
 Technology
MS Teams, Azure, O365
Technology
MS Teams, Azure, O365
 Type
Workshop
Type
Workshop
 Service Category
Adoption
Service Category
Adoption
 Duration
3 Days
Duration
3 Days
 Skill Set
Skill Set
O365
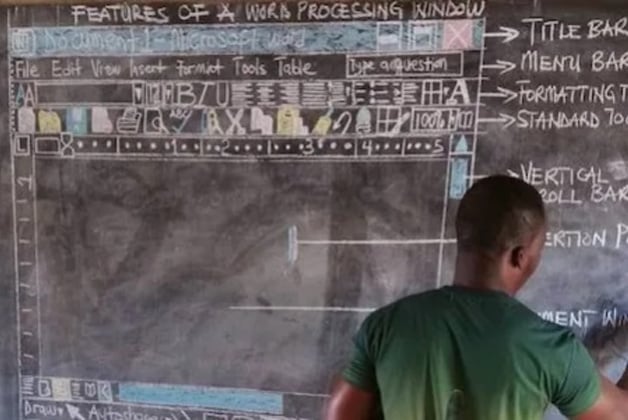
Designed as a three-day engagement, the Security Workshop enables SoHo to build an assessment intent for the deployment of advanced Microsoft Security workloads. The workshop uses a specialized Threat-Check SKU for identifying real-time threats in a customer environment, resulting in clear next steps and optimal risk mitigation. The workshop is intended to be delivered as a three-day engagement to:
- Understand customers’ security goals and objectives
- Identify security threats using a Microsoft 365 E5 trial
- Provide an overview of the Microsoft Security end-to-end story
- Showcase product capabilities through newly-designed rich demos
- Develop joint plans and recommend next steps
The Microsoft Security Workshop is an engagement that helps customers assess their security landscape and address their most pressing security goals and challenges, providing an immersive experience that brings the Microsoft security vision and capabilities to life.
In scope
The standard scope of this part of the engagement includes:
- Deployment of Microsoft 365 trial licenses for Threat Check in the customer tenant.
- Configuration of Microsoft 365 Security tools (Microsoft Threat Protection, Azure Active Directory Identity Protection, Office 365 Advanced Threat Protection, and Microsoft Cloud App Security) to discover threats to customers’ identity, email, and data, as per guidance provided in this document.
- Analysis of cloud applications deployed in the customer environment through the Cloud Discovery part of the Microsoft Cloud App Security and based on either Microsoft Defender ATP or on a one-time manual upload of logs from a single, on-premises perimeter security device, such as a firewall or proxy server.
- Detailed self-assessment of the customers’ security landscape and identification of top priorities, main influences, and opportunities to define the next steps.
- Security customer conversations covering an overview of Microsoft’s vision and security capabilities.
- Demonstration of Microsoft Threat-Protection solutions via key scenarios to help establish product value and key differentiators.
- Decommissioning of configuration and licenses at the end of the engagement.
Out of scope
The standard scope of this part of the engagement excludes anything that was not put in scope, in particular:
- Configuration of Microsoft 365 Security tools beyond the guidance provided in this document.
- Automatic upload of firewall or proxy server logs to Microsoft Cloud App Security (through Log Collector).
- Deep analysis (investigation) of threats found during the engagement.
- Forensic analysis.
- Technical designs or implementations.
- Proof-of-Concept or Lab Deployment
Security Workshop overview
Discover: Discovery Session & Threat Check Analysis
Envision: Microsoft Value Showcase: Customer Conversations, Enriched Security Demos
Plan: Next Steps Discussion, Existing workload deployment, Business value, Production Pilots
In addition to the Deployment Plan, customers will:
• Receive a documented security strategy for their teams and stakeholders.
• Better understand, prioritize, and mitigate potential threats.
• Work together with the delivery resource to define a list of next steps based on their needs, objectives, and results from the Security Workshop.
• Learn how they can accelerate their security journey together with Microsoft.

 Teams Video Conference
Teams Video Conference Murex
Murex Compliance
Compliance.png) Lucidchart to Visio
Lucidchart to Visio AI Consultation
AI Consultation